GetDNS
Exposed DNS servers can be used to redirect traffic to malicious websites and perform DNS spoofing attacks. Monitor DNS servers for unusual traffic and secure them with access controls and regular updates to prevent these attacks. This workflow will help you get all of the available DNS server for your ASN.
Complexity: intermediate
Category: Attack Surface Management
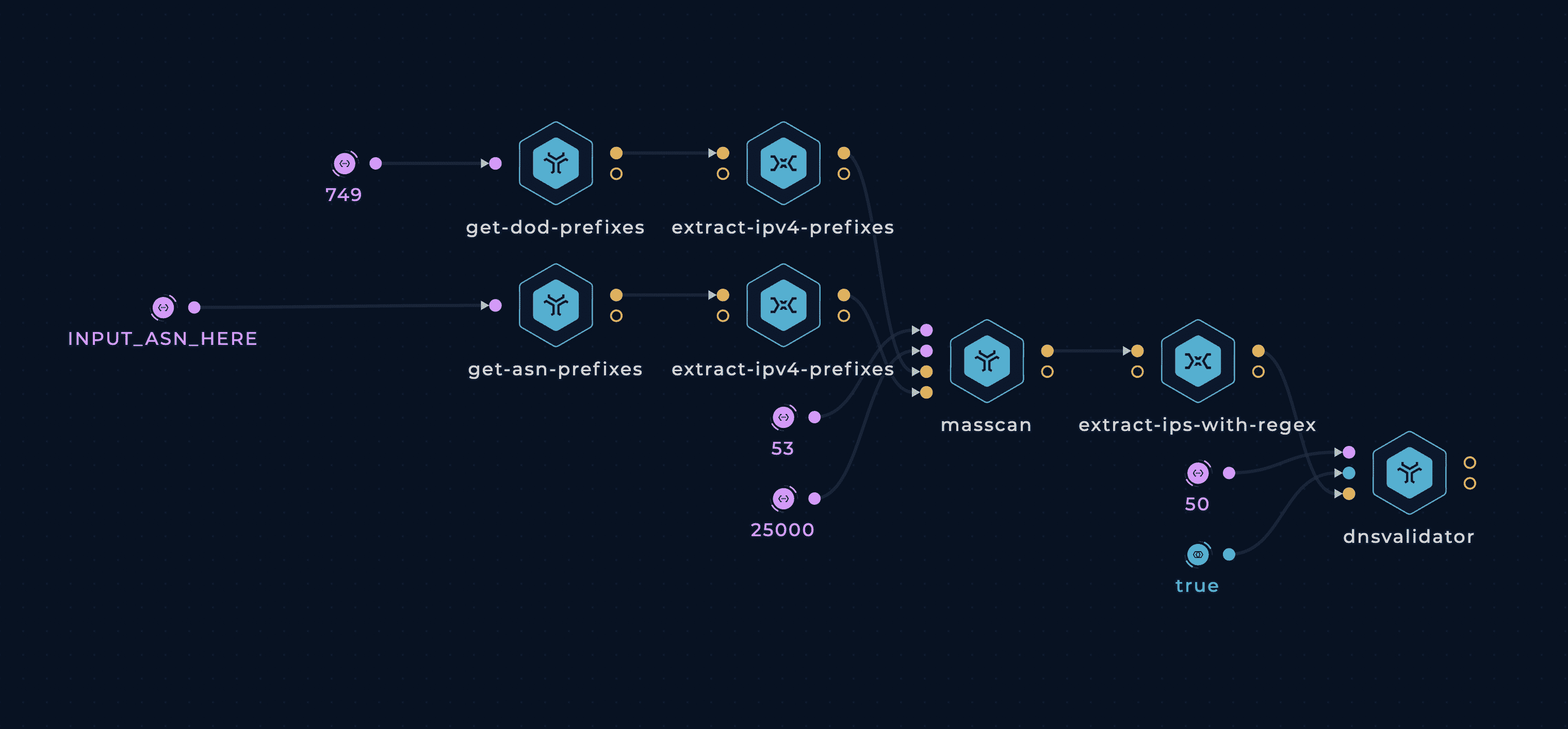
Workflow
Tools
Setup
You can set up this workflow by changing following input value:
- INPUT_ASN_HERE - provide a company's ASN, as a target
Workflow Targets Setup
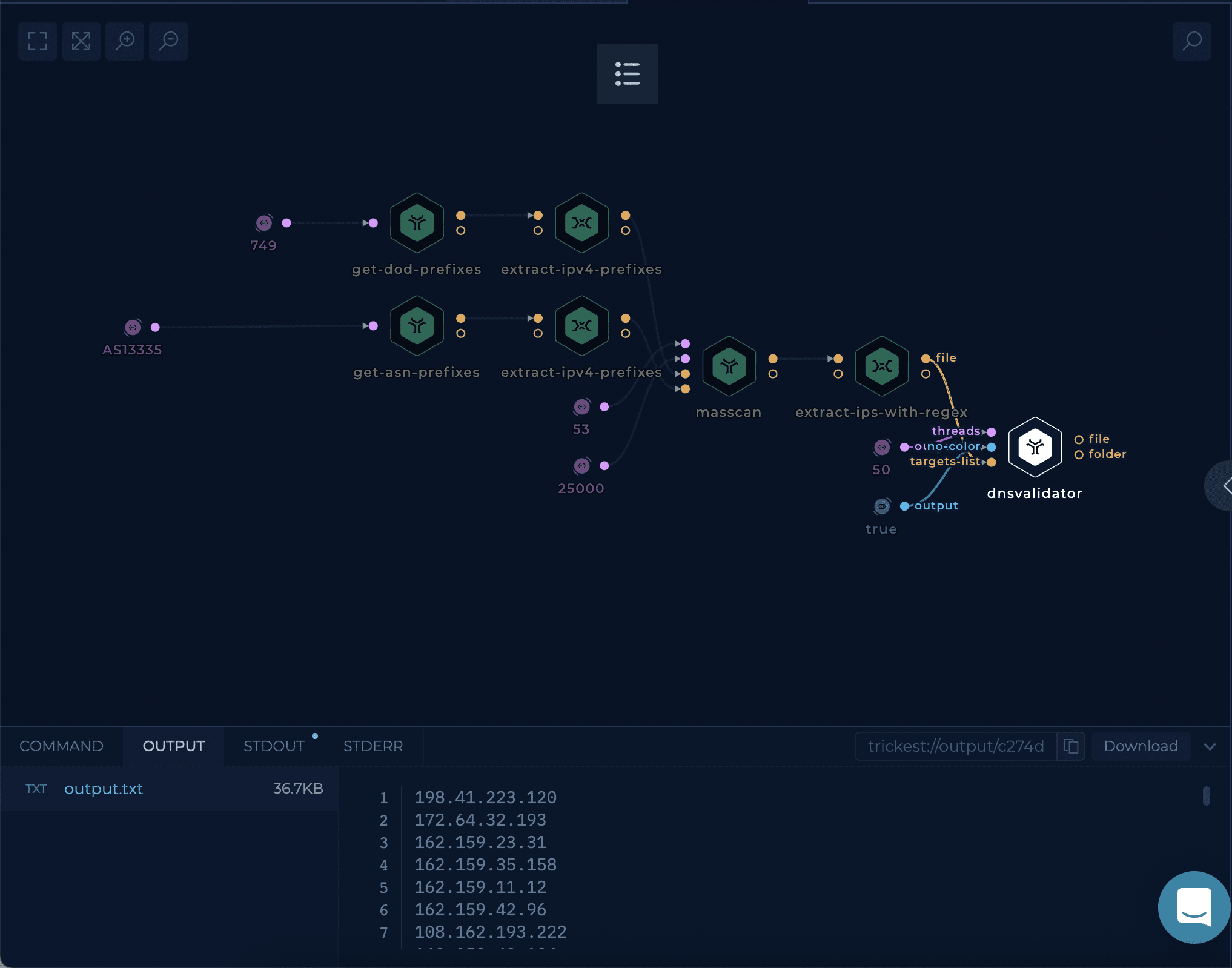
Execution and results
After setup workflow is ready to be executed. Once workflow's last node, dnsvalidator tool, is finished result can be viewed and downloaded.
The dnsvalidator tool will contain all of the found DNS Servers for a given ASN.
Try it out!
This workflow is available in the Library, you can copy it and execute it immediately!
Try out another Attack Surface Management Workflow - Get IPs and CNAMEs.
Improve this workflow
- Changing machine type of tools to speed up the execution
- Cover more ASNs by using-splitters
- Execute vulnerability checks on found DNS Servers