Overview
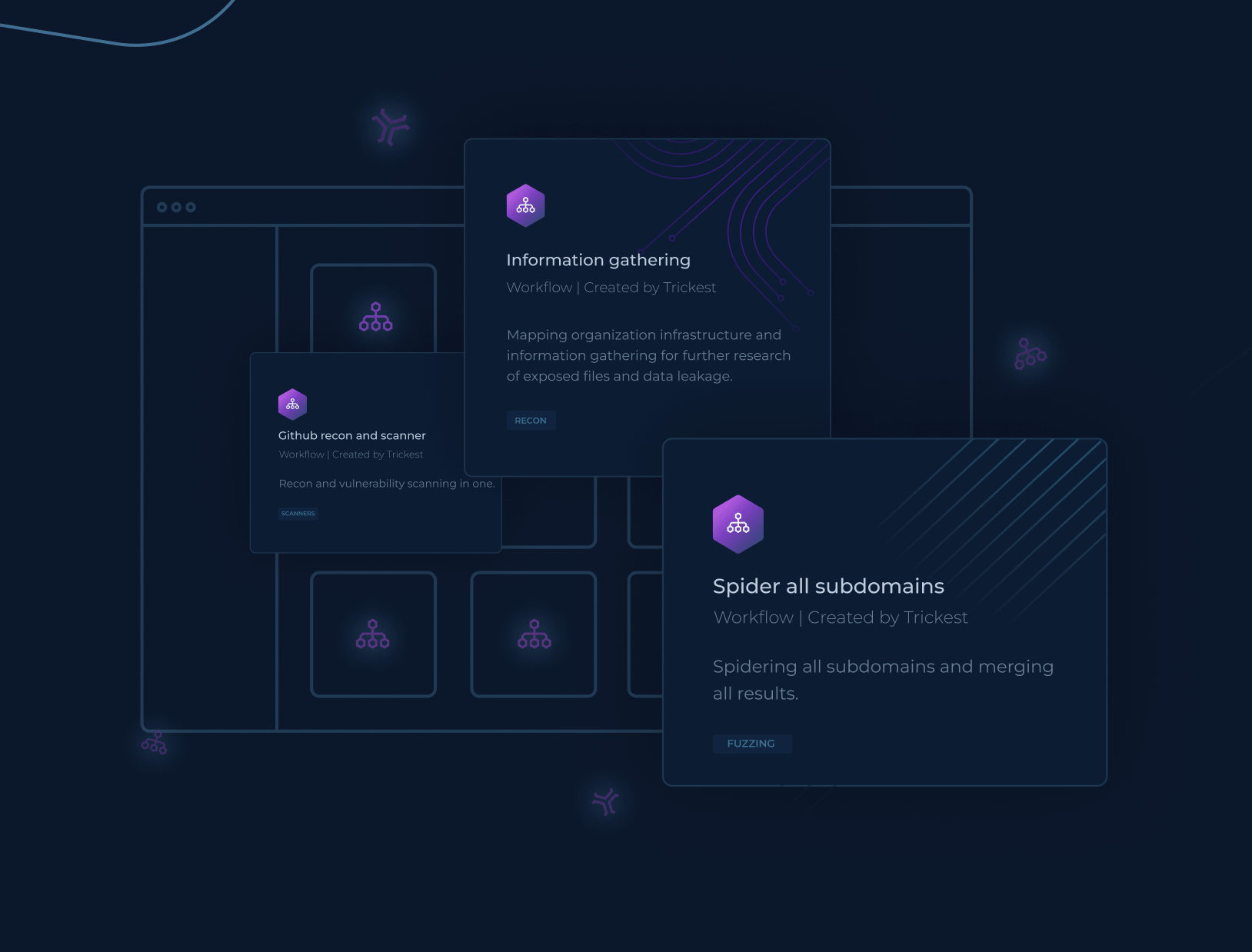
WORKFLOW TEMPLATES
Learn step-by-step how any of Trickest's pre-built workflows, powered by the most popular community tools, work and how to put it into practice.

TOOLS
Learn step-by-step how to use some of the most popular community tools in Trickest Platform.

SCRIPT
Learn step-by-step how to support tools with pre-built Trickest scripts, or to use scripts independently as a part of your workflows.

HOW-TO'S AND BEST PRACTICES
Learn step-by-step how to improve the performance of your tool/workflow.