Workflow Templates
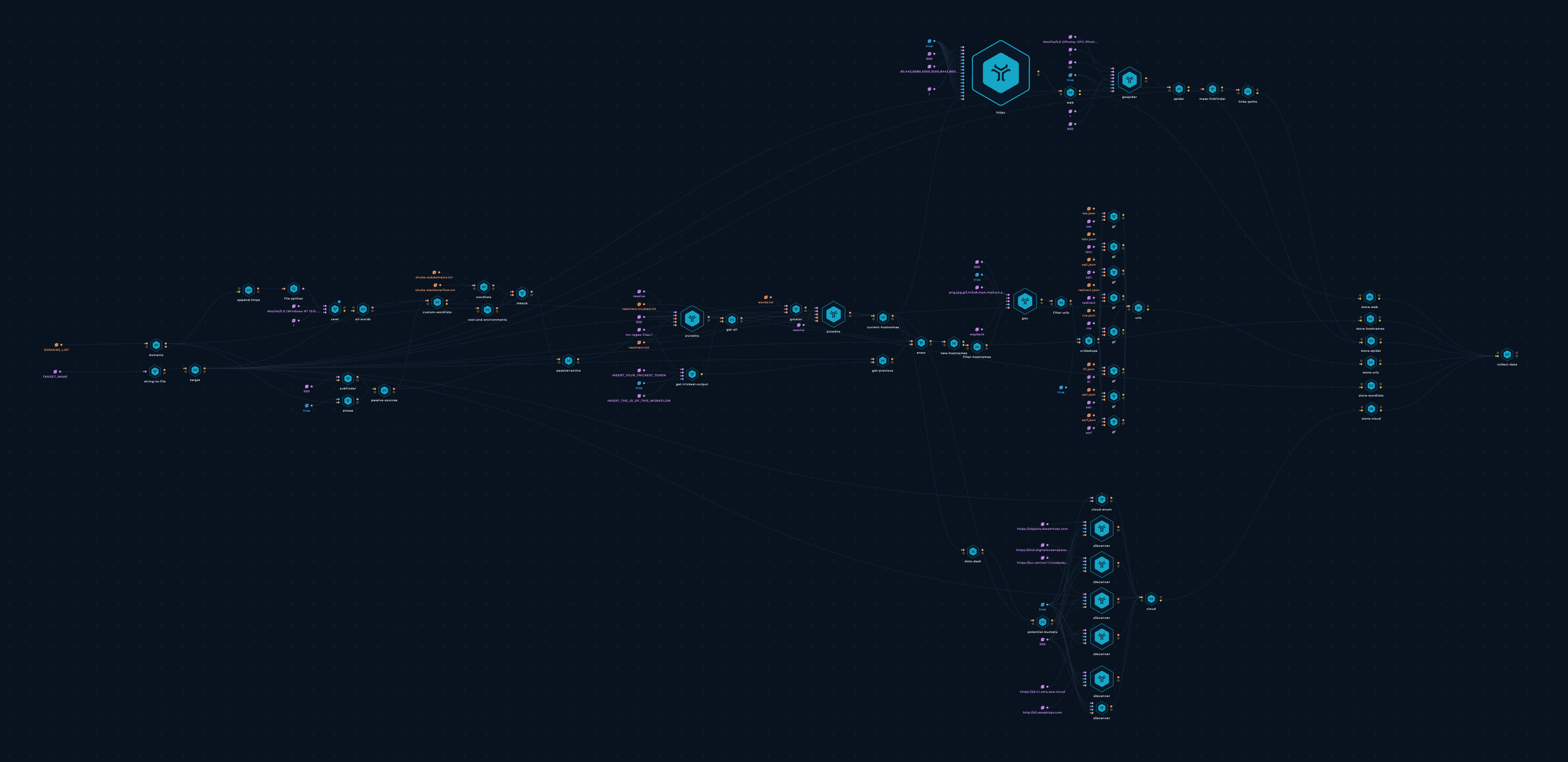
Attack Surface Management
Ready-to-go Trickest workflows for attack surface mapping.
Vulnerability Scan & Management
Ready-to-go Trickest workflows for vulnerability scanning. Scan outdated software, weak credentials, and misconfigurations.
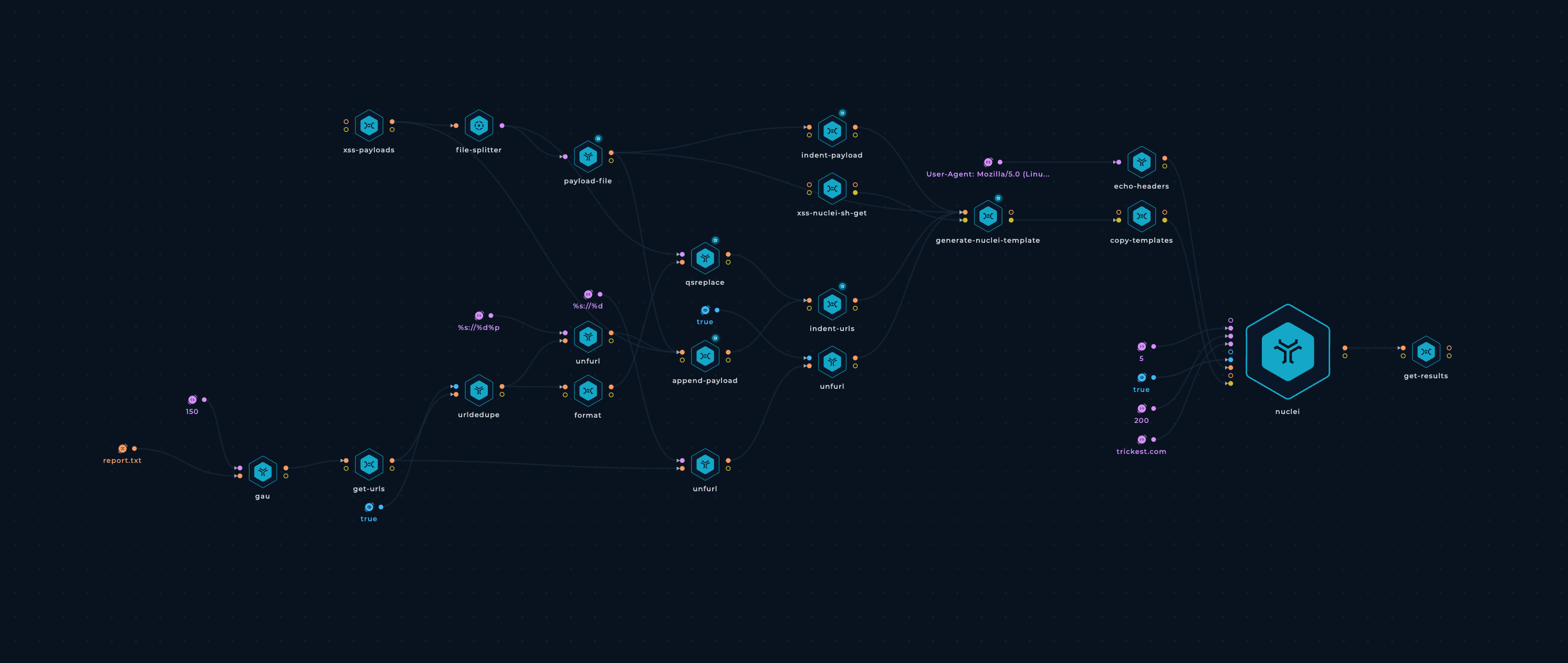
Secret Discovery
Ready-to-go Trickest workflows for automated secret discovery. Find exposed API secrets, tokens, passwords, and keys with ease.

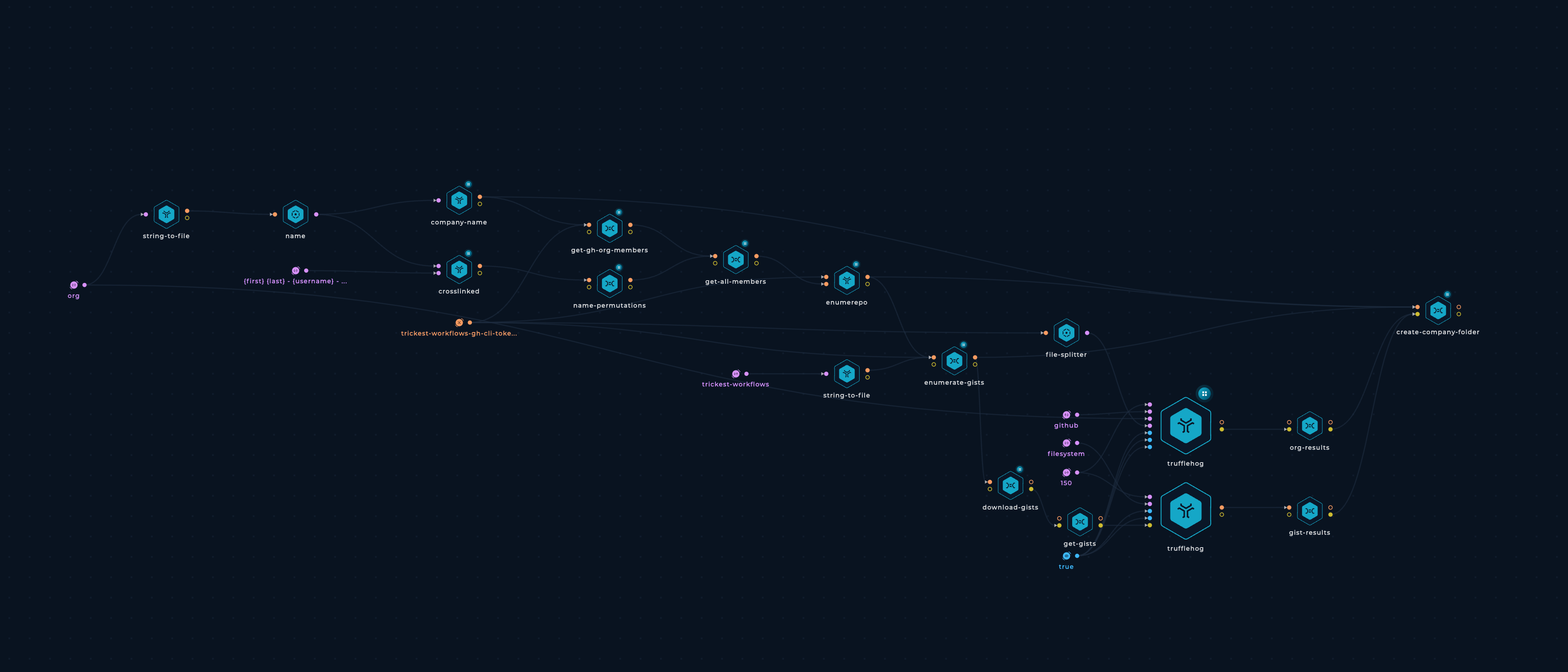
Threat Intelligence
Ready-to-go Trickest workflows for streamlining the process of collecting, analyzing, and disseminating information about threats to an organization.
Utilities
Ready-to-go Trickest workflows for generating data used in further research.
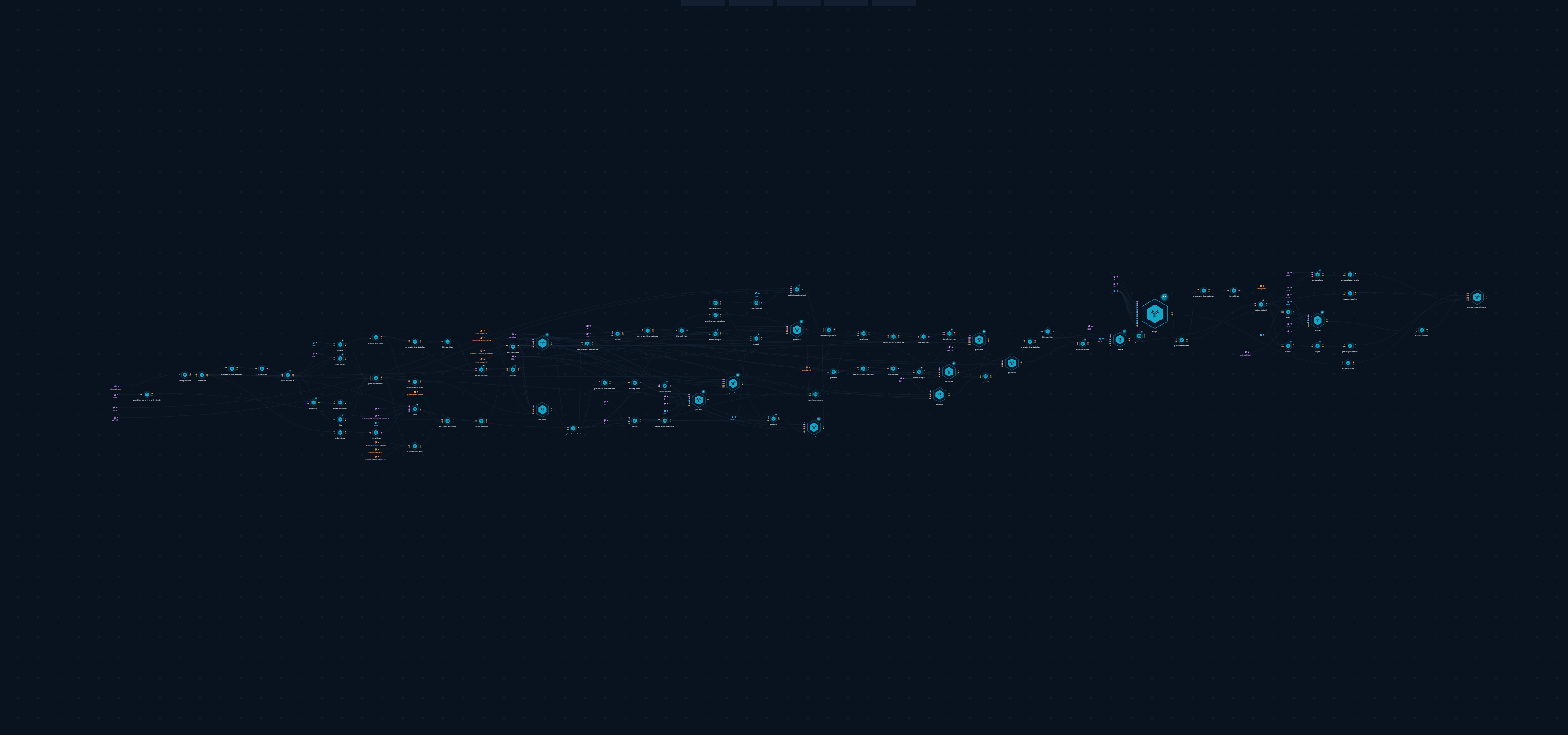
Web Discovery
Ready-to-go Trickest workflows for gathering information on web applications, Web Servers, URLs, and exposed admin panels.

Mobile
Ready-to-go Trickest workflows for gathering information on mobile applications.