THE PLATFORM
OFFENSIVE
SECURITY
WORKFLOWS
Join us in our mission to democratize offensive security with tailored best-in-class solutions that address the unique needs of professionals and organizations.
Trusted By
Trickest Experience
Empowering ethical hackers
all over the world
Eric Head todayisnew
#1 Bug Bounty Hunter
@ Hackerone/Bugcrowd
The platform was able to find assets other miss, quickly, with amazing support and genuinely kind and skilled team.
Carlos Polop Martin
Author @ HackTricks &
Team Leader @ Halborn
Doing security research with Trickest is just simpler and faster. I can focus on creating workflows, analyzing the results, and forget about installation and infrastructure problems.
Luke Stephens Hakluke
Ethical Hacker &
Creator @ haksec.io
The Trickest platform is flexible enough to allow human creativity to shine while removing the pain of managing scalable infrastructure. The workflow UI is so beautifully designed that building out security workflows is a pleasure.
Alexis Fernández six2dez
Creator of reconFTW &
Red Team Engineer @ Visma
Trickest is the only platform that allows me to take recon to the next level. It gives me maximum freedom to build the workflow I want.
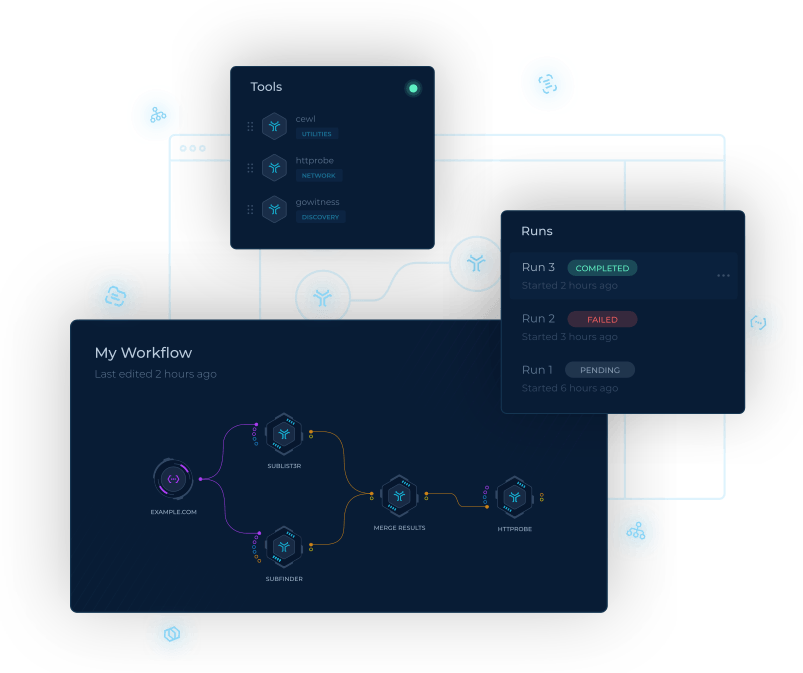
workflow automation
BUILD, EDIT, AND RUN WORKFLOWS
Evolve from the terminal to a specialised IDE for offensive security. Use Trickest’s library of tool nodes, import your own scripts, or drop in your favourite open-source tools – all in one place.
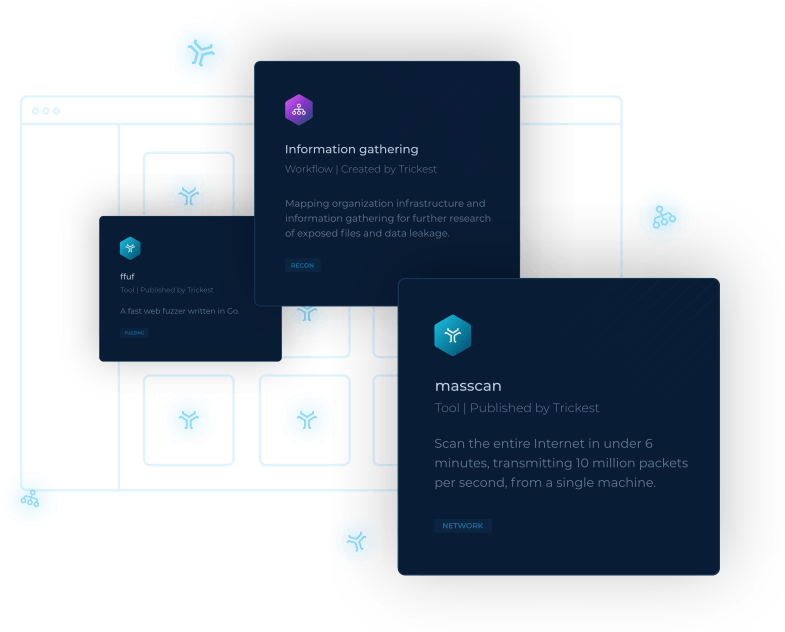
store
READY-MADE TOOLS AND WORKFLOWS
Don’t feel like building from scratch? Choose from template workflows for common tasks and a growing list of 300+ open source tools the security community loves.
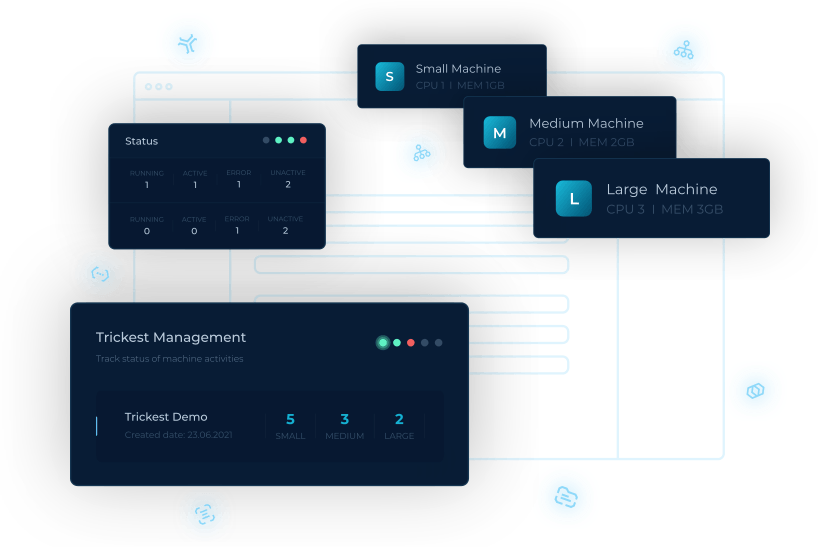
cloud service
RUN, SCALE, AND OPTIMIZE WITH EASE
Run your workflows in the cloud with easy autoscaling and cost controls. Skip manual infrastructure setup and stop paying for idle VPSs.
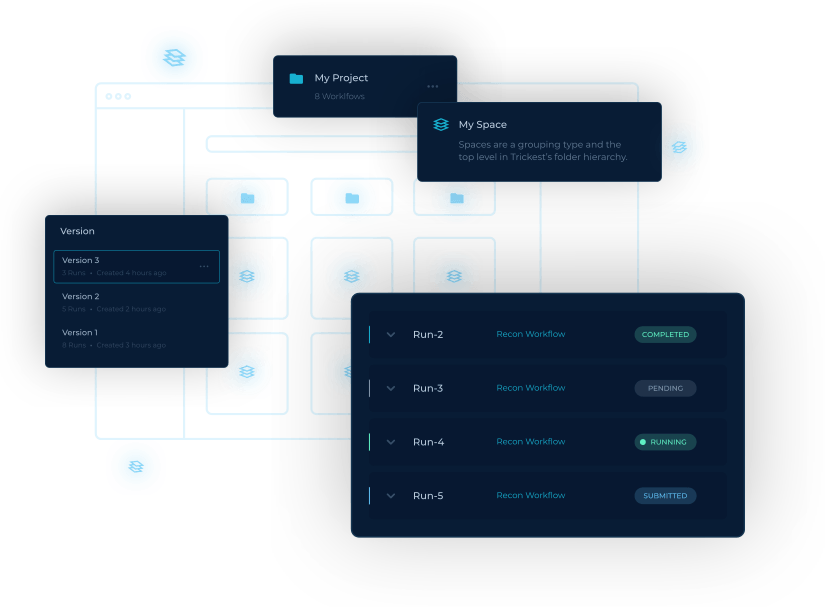
project management
ORGANIZE WORK AND LOSE NOTHING
No more digging through filesystems for your old runs – use Trickest’s Spaces, Projects, and Workflow versioning to stay on top of even the most complex projects.
Who is Trickest for?
Anyone who interacts with offensive security: enterprise security teams, red teams, purple teams, specialized pentesters, bug bounty hunters, security researchers, educators, etc.
Why is Trickest better than other solutions?
Most other solutions focus on blackbox scanners, event management, and monitoring that make it difficult to understand what is happening under the hood. Trickest workflows are fully customizable and make it easy to understand step-by-step pentesting or SecOps logic.
Can beginners use Trickest?
Yes – the platform’s low-code possibilities and detailed documentation make it a great option for newcomers and learners.
Does Trickest replace pentesters?
Yes and No – for companies, pre-packaged workflows in the Trickest Library make it easy to run standard pentests that may be required for e.g. compliance purposes. Still, the real power of Trickest is in the hands of pentesters or other security professionals who can use the platform to do their jobs more efficiently.
Does Trickest integrate with other products?
We plan to release 3rd-party integrations in the near future.
Can I add new tools to the Trickest platform?
If you are a Business user, you can do it in the platform as your Private Tools.
If you are a Community user – send us an email at support@trickest.com, and we’ll integrate it as soon as possible.
Does Trickest work for teams?
Yes – the platform’s workspaces, search, and versioning make it a great choice for security teams small and large. We plan to introduce dedicated collaboration features in future releases.
How can I try the Trickest platform?
You can Sign Up and choose the profile you want to test it for.
Blog
Explore our blog
Learn more about offensive cybersecurity with Trickest workflows.
GET STARTED WITH TRICKEST TODAY
Complete our registration to elevate and automate your offensive security endeavors.
Get started