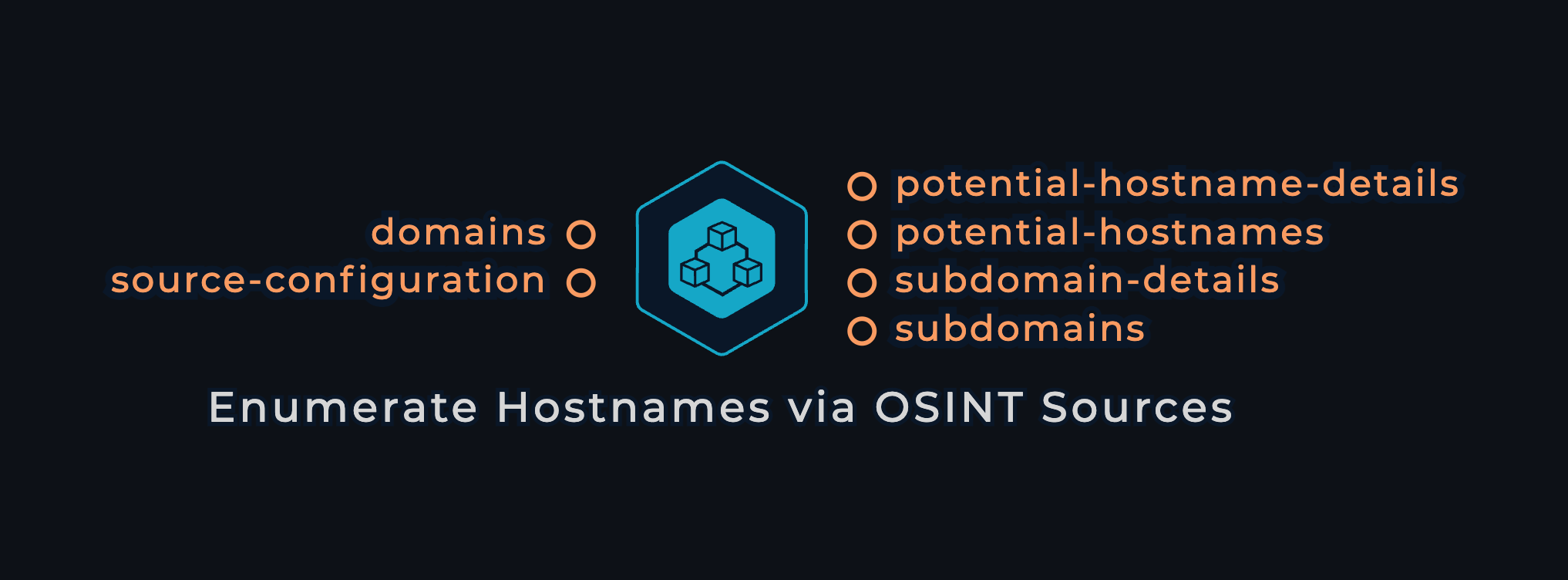
About the module
This module enumerates subdomains for a list of domains without interacting with name servers. Instead, it uses carefully chosen and tuned data sources to balance speed and thoroughness. It can also identify extra root domains and hostnames linked to the specified target domains, even if they aren’t their subdomains. You don't need any 3rd-party API keys to use this module, but if you choose to query more data sources, you can give it that extra boost.
Module Screenshot
Features
- Carefully curated and optimized data sources ensure a balance between speed and comprehensiveness.
- Can enumerate thousands of domains simultaneously.
- Capable of identifying not only subdomains but also additional hostnames and root domains associated with the target organization.
- Functional without any API keys, but offers the option to provide them to improve results.
- Includes a detailed output file showing which data sources found each subdomain, helping you learn more.
Inputs
Required
- domains: a list of domain names:
example.com
Optional
source-configuration: YAML file with API keys to query more data sources.
github:
- GITHUB_API_KEY_1
- GITHUB_API_KEY_2
shodan:
- SHODAN_API_KEY
# supported sources:
# - alienvault
# - anubis
# - bevigil
# - binaryedge
# - bufferover
# - c99
# - censys
# - certspotter
# - chaos
# - chinaz
# - commoncrawl
# - crtsh
# - digitorus
# - dnsdb
# - dnsdumpster
# - dnsrepo
# - fofa
# - fullhunt
# - github
# - hackertarget
# - hunter
# - intelx
# - netlas
# - leakix
# - passivetotal
# - quake
# - rapiddns
# - redhuntlabs
# - robtex
# - securitytrails
# - shodan
# - sitedossier
# - threatbook
# - virustotal
# - waybackarchive
# - whoisxmlapi
# - zoomeyeapi
# - facebook
# - builtwith
Changelog
v1.0.0 Initial release
Process
This module starts by distributing the list of domains among the designated machines for parallel processing. Each machine receives a portion of domains and an enumeration technique to execute. After processing all domains with the selected data sources, the results are consolidated.
Next, the scope is reviewed to generate the subdomains and potential-hostnames outputs, excluding any known out-of-scope domains. Finally, the discovered hostnames are organized into JSON records, along with information about the sources that detected them into the hostnames-detailed output.
Outputs
- subdomains: a list of found subdomains
foo.example.com
bar.example.com
- subdomain-details: JSONLines records showing additional information about each potential hostname, such as the data source it was found through
{"hostname": "foo.example.com", data_source: "shodan"}
{"hostname": "bar.example.com", data_source: "github"}
- **potential-hostnames: **a list of associated hostnames that don’t strictly fall in the scope
test.example-internal.com
admin.example.com
- potential-hostname-details: JSONLines records showing additional information about each potential hostname, such as the data source it was found through
{"hostname": "admin.example.com", data_source: "cloud tls certificate"}
{"hostname": "test.example-internal.com", data_source: "certificate transparency"}